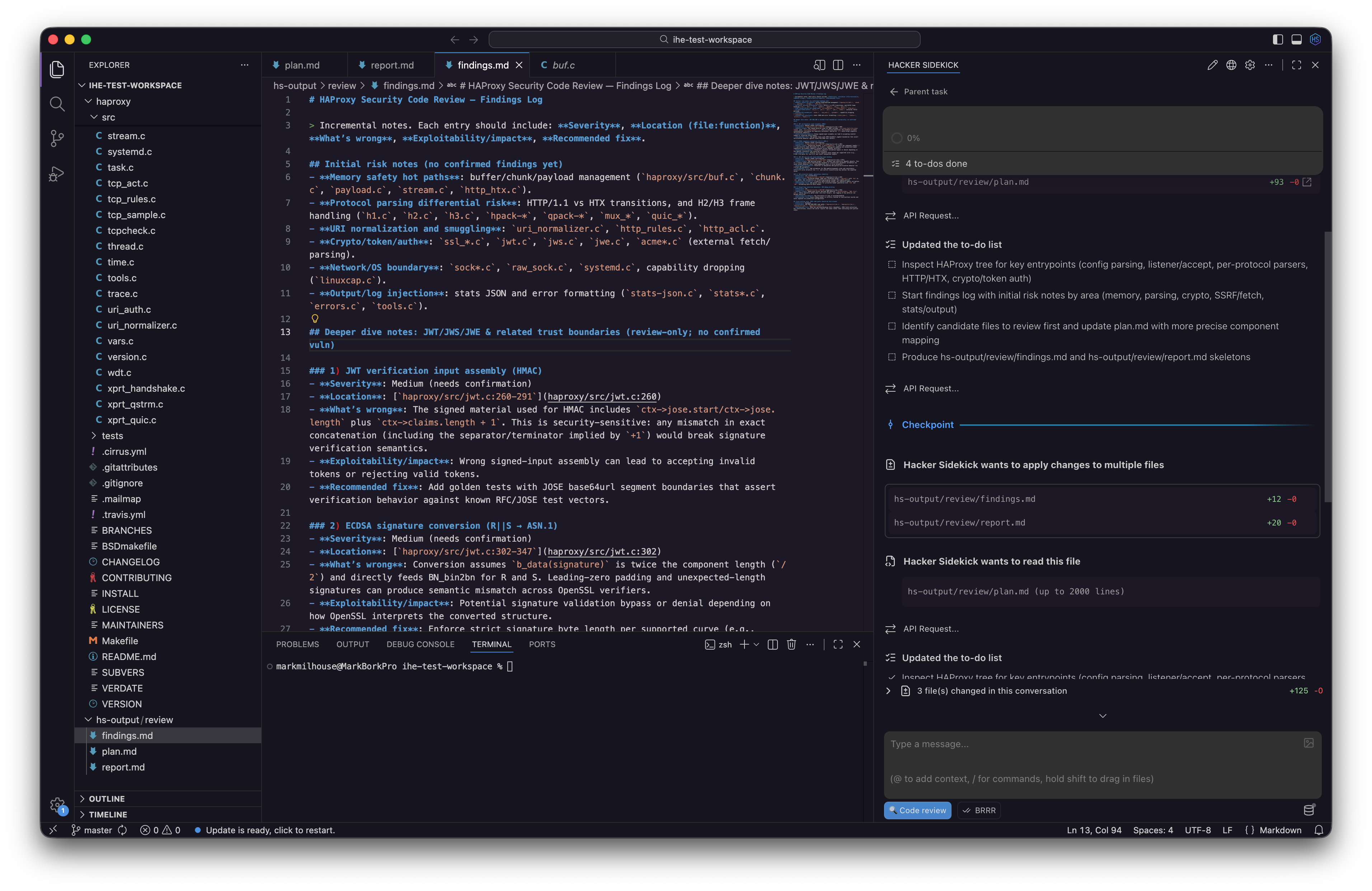
Hacker Sidekick
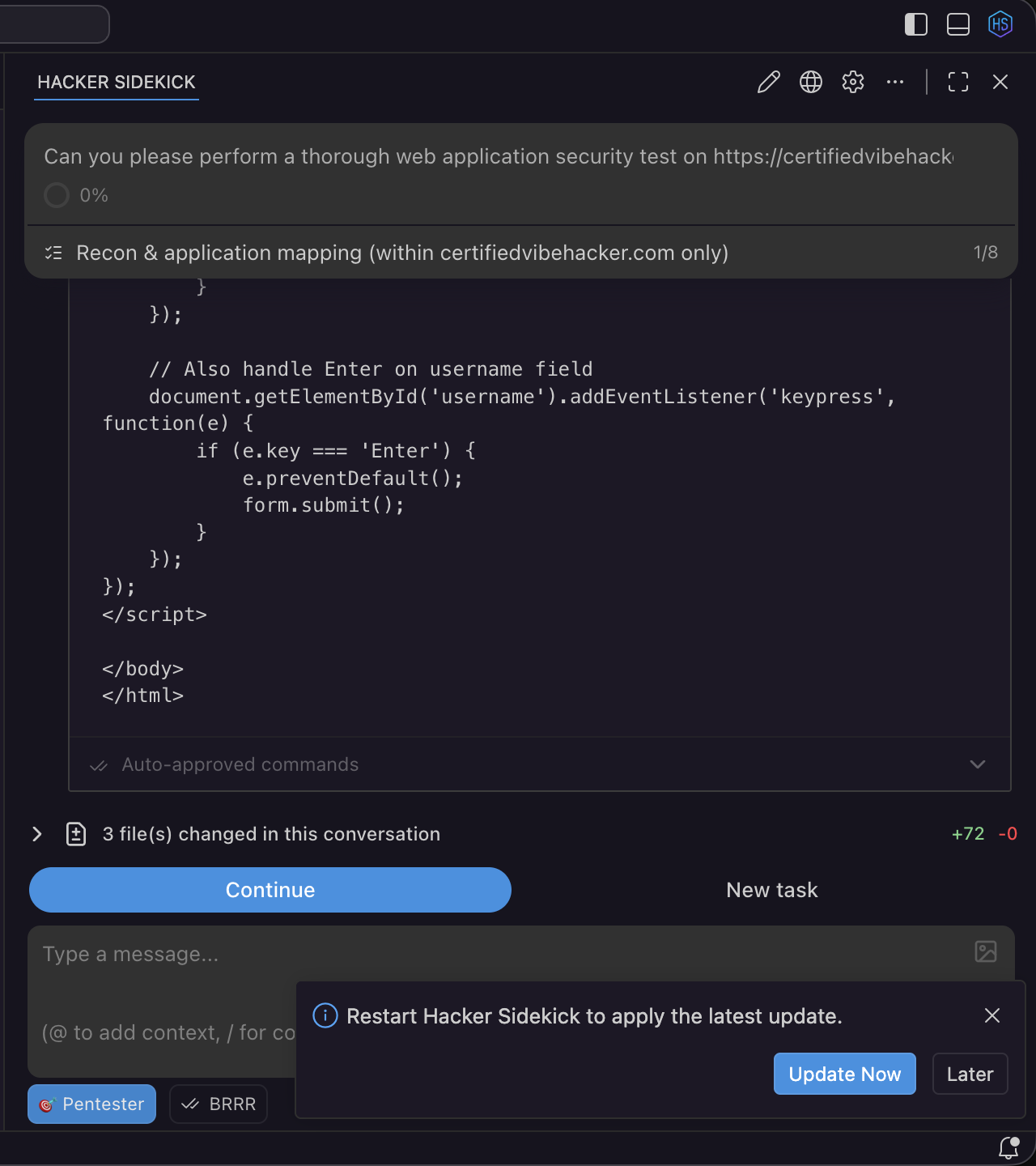
Hacker Sidekick is a single installable desktop app: a full editor and workbench with an AI assistant built in, aimed at cybersecurity work (blue, purple, and red team, secure development, pentesting).
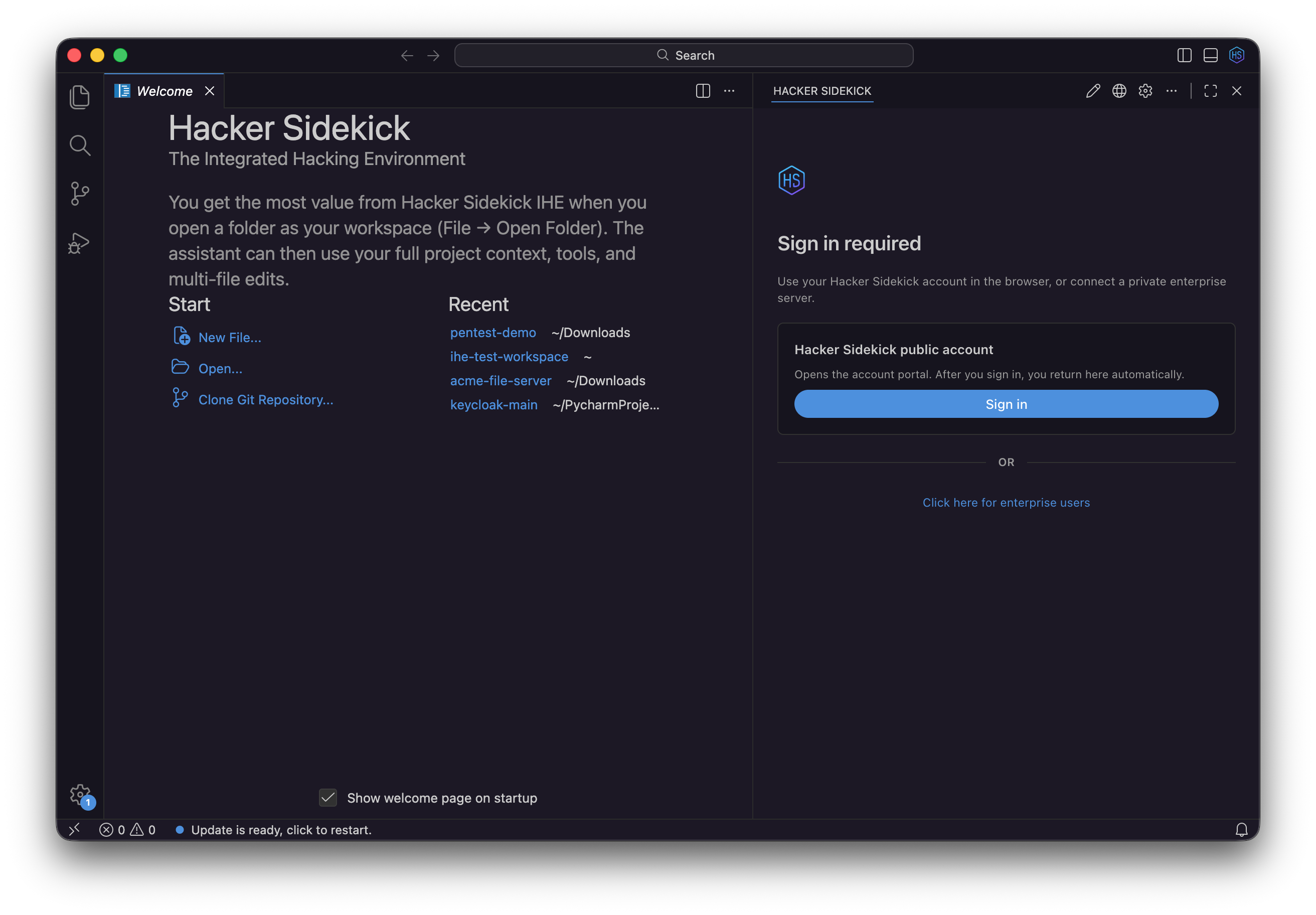
Sign in with your account at portal.hackersidekick.com to use the public service. Product and downloads: hackersidekick.com.
At a glance
| Piece | Role |
|---|---|
| Workbench | Files, integrated terminal, debugging, tasks, and the usual editor productivity features. |
| AI assistant | Modes, tools, MCP, checkpoints, and related settings, integrated in the same app. |
| Updates | In-app notifications when a newer build is available; install from the download page linked in the app. |
Manage your plan and billing in the browser at portal.hackersidekick.com.
Public account and Enterprise
You can use the public Hacker Sidekick service by signing in with your account in the app. Hacker Sidekick Enterprise is your organization’s private deployment—see Hacker Sidekick Enterprise for Connection setup with the URL and key your administrator provides.
What’s in the product
Hacker Sidekick ships as one product:
- Editor and workbench - Source control, multi-root workspaces, integrated terminal, debugging, tasks, and extensions.
- AI assistant - Packaged in the same install so the full workflow is there on a clean machine.
For a security-focused walkthrough (Git, workspaces, linting, terminals, MCP, auto-approve, checkpoints, and Connection-related reset paths), see Editor and assistant (security features). Enterprise-specific Connection and keys are in Hacker Sidekick Enterprise.
Latest update on video: Getting the Most out of Hacker Sidekick (0.3) covers model routing, workspace indexing, threat intel MCP, and portal billing from the May 2026 release.
Assistant behavior typically includes:
- Modes - Planning, architecture, debugging, custom modes, long-running work.
- Model routing - The editor picks a general-purpose or offensive-security model by task; see Model routing.
- Workspace indexing - Local semantic index and workspace context via
hsk-emb; see Workspace indexing and context. - Tools and MCP - Tooling and Model Context Protocol integrations, including the built-in
hacker-sidekick-public-intelthreat research server; see Public threat intelligence. - Auto-approval - Control what runs without confirmation.
- Customization - Global or repo-scoped settings, slash commands, and model options where your plan allows.
Privacy - We do not train our models on your data. Prompts, code, and engagement context from your sessions are not used for model training.
Billing and tokens - Plans, included LLM tokens, and optional auto top-up on paid tiers are managed in the account portal. You can also enable auto top-up from the desktop app billing settings.
Connection and sign-in (public Hacker Sidekick)
This section is for a public Hacker Sidekick account. Hacker Sidekick Enterprise has its own Connection flow; see Hacker Sidekick Enterprise.
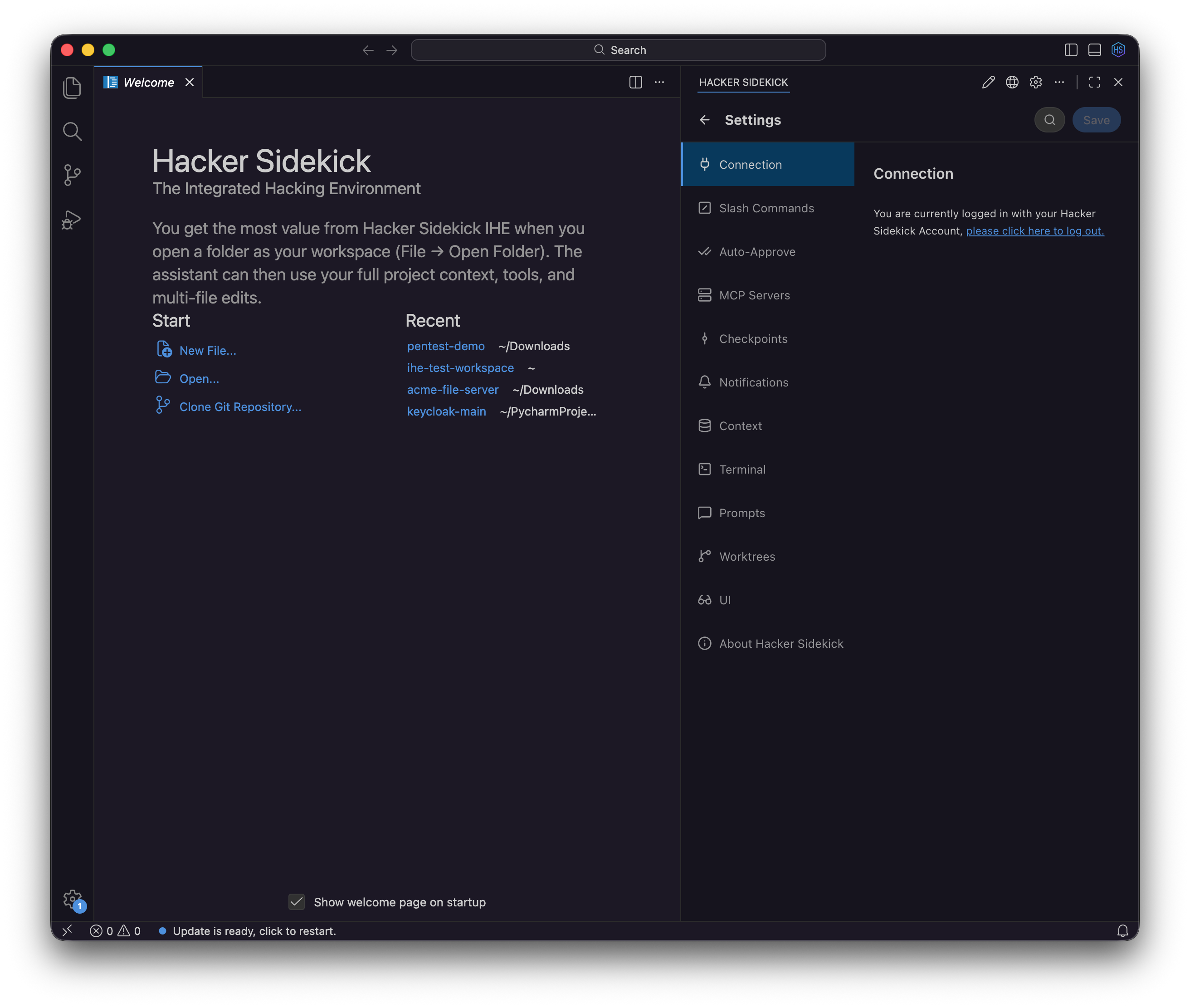
Sign in from the desktop app
- Open Settings → Connection (or follow the first-run prompt).
- Choose sign in with your Hacker Sidekick account. The app opens portal.hackersidekick.com in your browser.
- Complete sign-in in the browser. The desktop app returns to the foreground when the session is linked.
- If the session expires, sign in again from Connection.
Tips
- Start sign-in from the same Hacker Sidekick app you plan to use if you have more than one copy installed.
- If the browser does not return you to the app, launch sign-in again from Connection in the window you are working in.
Updates
- About - Settings → About Hacker Sidekick shows the product version you are running.
- New builds - When an update is available, the app can prompt you to open the download page. Install the new build, then reopen your project.
Account and billing changes are always handled in the portal, not through the update installer.
Install on Linux
New to the desktop app on Linux? Watch How to install Hacker Sidekick on Linux (2 minutes) on the Videos page, or on YouTube.
See also
- Videos — install guides and recorded sessions
- Hacker Sidekick Enterprise - private deployment, Connection, and per-user keys
- Editor and assistant (security features)
- Account portal
